December 17, 2019
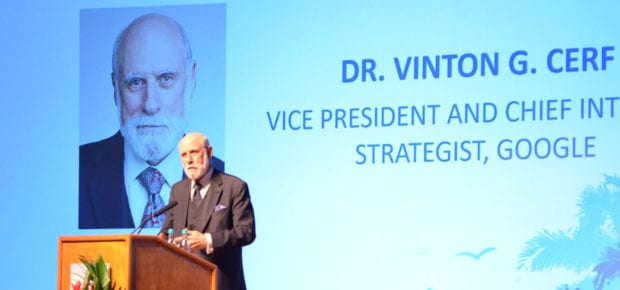
When designing software that powers the latest Internet of Things (IoT) devices, technologists need to solve for possible issues that may come up today, but also anticipate future challenges. At the IEEE GLOBECOM 2019 conference in Waikoloa, HI, IEEE Life Fellow Vinton Cerf spoke on the importance of designing resilient IoT software to provide adequate privacy and security for the entire lifespan of an IoT device – up to 10 years in some cases.
Cerf, who currently serves as Vice President and Chief Internet Strategist at Google, is a co-designer of Transmission Control Protocol/Internet Protocol (TCP/IP), which allows computers to communicate with one another. Cerf is widely regarded as one of the “fathers of the internet, ” and posed several ethical questions during the conference on how we can build secure and scalable IoT systems.
Vinton Cerf’s Recommendations for Ethical and Secure IoT Software Design
How do we write code without bugs? How do we fix bugs once an IoT device has shipped? How do we validate IoT software updates, and guarantee that they have been tested and are certified?
“We can no longer afford to treat software bugs as just mistakes,” says Cerf. “We have a responsibility as engineers to be very thoughtful about how we design and build IoT systems.”
AI-controlled devices in our homes and industrial settings pose a significant hazard, and something all engineers should be mindful of during their design and production process.
“Machine learning (ML) is not the hazard,” explains Cerf. “The real hazard is software that bugs in IoT devices. When there are corner cases that ML has not been exposed to, it will make mistakes. To avoid hazards, we should not give ML too much autonomy.”
Cerf also suggests building IoT systems that can perform diagnostics and anticipate failures before they happen.
“Authentication and public key cryptography are central to IoT systems,” says Cerf. “We need to demonstrate resistance against external attacks, and we need to be able to recover after major failure.”
See also Passwords, Multi-Factor Authentication and Cybersecurity
When asked what he would do differently if he could go back and redesign the internet, Cerf noted that nobody predicted mobile devices back in 1973 when computers occupied entire rooms.
“Had we known how large the internet would get, we would have started with IPv6, (Internet Protocol Version 6) and given devices unique identifiers at the TCP layer,” says Cerf. “We also should have implemented public key cryptography much earlier.”
As IoT continues to grow in unexpected ways, engineers must focus on designing ethical, resilient and secure devices that will protect consumers from bugs or cyber attacks.
About our author
Mario Milicevic is an IEEE Member and Staff Communication Systems Engineer at MaxLinear.




 Liquid Infrastructure: Our Planet's Most Precious Resource
Liquid Infrastructure: Our Planet's Most Precious Resource The Impact of Technology in 2025
The Impact of Technology in 2025 Quantum and AI: Safeguards or Threats to Cybersecurity?
Quantum and AI: Safeguards or Threats to Cybersecurity? Why AI Can't Live Without Us
Why AI Can't Live Without Us Bits, Bytes, Buildings and Bridges: Digital-Driven Infrastructure
Bits, Bytes, Buildings and Bridges: Digital-Driven Infrastructure Impact of Technology in 2024
Impact of Technology in 2024 Emerging AI Cybersecurity Challenges and Solutions
Emerging AI Cybersecurity Challenges and Solutions The Skies are Unlimited
The Skies are Unlimited Smart Cities 2030: How Tech is Reshaping Urbanscapes
Smart Cities 2030: How Tech is Reshaping Urbanscapes Impact of Technology 2023
Impact of Technology 2023 Cybersecurity for Life-Changing Innovations
Cybersecurity for Life-Changing Innovations Smarter Wearables Healthier Life
Smarter Wearables Healthier Life Infrastructure In Motion
Infrastructure In Motion The Impact of Tech in 2022 and Beyond
The Impact of Tech in 2022 and Beyond Cybersecurity, Technology and Protecting Our World
Cybersecurity, Technology and Protecting Our World How Technology Helps us Understand Our Health and Wellness
How Technology Helps us Understand Our Health and Wellness The Resilience of Humanity
The Resilience of Humanity Harnessing and Sustaining our Natural Resources
Harnessing and Sustaining our Natural Resources Creating Healthy Spaces Through Technology
Creating Healthy Spaces Through Technology Exceptional Infrastructure Challenges, Technology and Humanity
Exceptional Infrastructure Challenges, Technology and Humanity The Global Impact of IEEE's 802 Standards
The Global Impact of IEEE's 802 Standards Scenes of our Cyber Lives: The Security Threats and Technology Solutions Protecting Us
Scenes of our Cyber Lives: The Security Threats and Technology Solutions Protecting Us How Millennial Parents are Embracing Health and Wellness Technologies for Their Generation Alpha Kids
How Millennial Parents are Embracing Health and Wellness Technologies for Their Generation Alpha Kids Space Exploration, Technology and Our Lives
Space Exploration, Technology and Our Lives Global Innovation and the Environment
Global Innovation and the Environment How Technology, Privacy and Security are Changing Each Other (And Us)
How Technology, Privacy and Security are Changing Each Other (And Us) Find us in booth 31506, LVCC South Hall 3 and experience the Technology Moon Walk
Find us in booth 31506, LVCC South Hall 3 and experience the Technology Moon Walk Virtual and Mixed Reality
Virtual and Mixed Reality How Robots are Improving our Health
How Robots are Improving our Health IEEE Experts and the Robots They are Teaching
IEEE Experts and the Robots They are Teaching See how millennial parents around the world see AI impacting the lives of their tech-infused offspring
See how millennial parents around the world see AI impacting the lives of their tech-infused offspring Take the journey from farm to table and learn how IoT will help us reach the rising demand for food production
Take the journey from farm to table and learn how IoT will help us reach the rising demand for food production Watch technical experts discuss the latest cyber threats
Watch technical experts discuss the latest cyber threats Explore how researchers, teachers, explorers, healthcare and medical professionals use immersive technologies
Explore how researchers, teachers, explorers, healthcare and medical professionals use immersive technologies Follow the timeline to see how Generation AI will be impacted by technology
Follow the timeline to see how Generation AI will be impacted by technology Learn how your IoT data can be used by experiencing a day in a connected life
Learn how your IoT data can be used by experiencing a day in a connected life Listen to technical experts discuss the biggest security threats today
Listen to technical experts discuss the biggest security threats today See how tech has influenced and evolved with the Games
See how tech has influenced and evolved with the Games Enter our virtual home to explore the IoT (Internet of Things) technologies
Enter our virtual home to explore the IoT (Internet of Things) technologies Explore an interactive map showcasing exciting innovations in robotics
Explore an interactive map showcasing exciting innovations in robotics Interactively explore A.I. in recent Hollywood movies
Interactively explore A.I. in recent Hollywood movies Get immersed in technologies that will improve patients' lives
Get immersed in technologies that will improve patients' lives